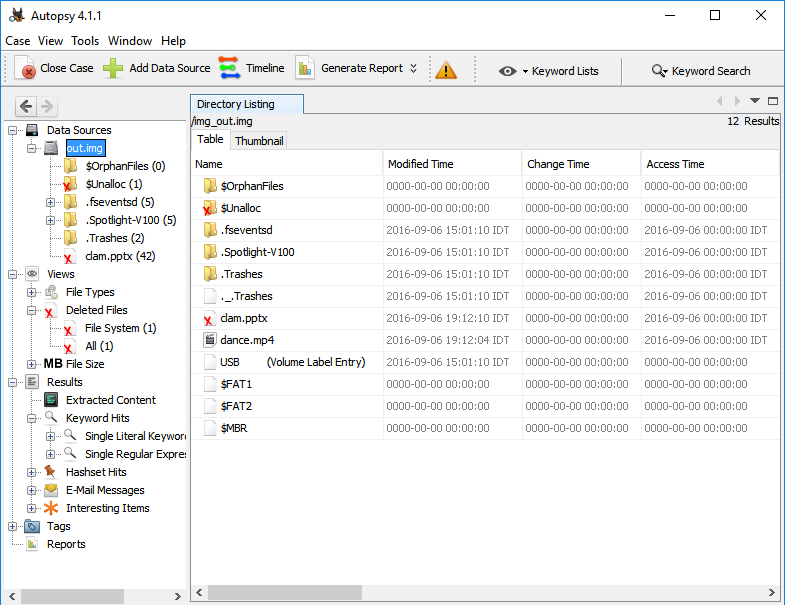
Update (2020): Since writing this article, it has become, in a way, the go-to tutorial for learning radare2. Your feedback was amazing and I am very happy for the opportunity to teach new people about radare2.
A lot has changed since I wrote this tutorial, both with radare2 and with me. I am now, for several years, a core member in the radare2 team and a maintainer of Cutter, a modern, GUI-based, reverse engineering framework that is powered by radare2.
This is an updated version of the original tutorial. I will keep it updated every now and then to make sure it is up-to-date with the changes in radare2.
Enjoy!
Prologue
I was playing a lot with radare2 in the past years, ever since I began participating in CTFs and got deeper into RE and exploitation challenges. I found radare2 very helpful with many CTFs tasks and my solutions had shortened significantly. It’s also my go-to tool for malware analysis tasks such as configuration retrievals. Sadly, I believe that only few people are familiar with radare2. It might be because they’re afraid to break out of their comfort zone (IDA Pro, x64dbg, Ghidra, OllyDBG, gdb) or they have simply not heard of it. Either way, I honestly believe that you must include radare2 in your toolbox.
Because I got really enthusiastic about the project and I want more and more researchers to be familiar with it, use it and hopefully contribute to the project, I decided to create a series of articles and use-cases of r2. Since these articles aim to teach you the basics of radare2, its features, and capabilities, I’ll explain much more than you actually need to know in order to solve each task.

radare2
radare2 is an open-source framework for reverse engineering and binary analysis which implements a rich command-line interface for disassembling, analyzing data, patching binaries, comparing data, searching, replacing, visualizing and more. It has great scripting capabilities, it runs on all major platforms (GNU/Linux, Windows, *BSD, iOS, OSX, Solaris…) and it supports tons of architectures and file formats. But maybe above all of its features stands the ideology – radare2 is absolutely free.
This framework is composed of a set of utilities that can be used either together from r2 shell or independently – We’ll get familiar with tools such as rahash2, rabin2 and ragg2. Together they create one of the most powerful toolsets in the field of static and dynamic analysis, hex editing and exploitation (in the following articles I’ll dive deeper into developing exploits using radare2).
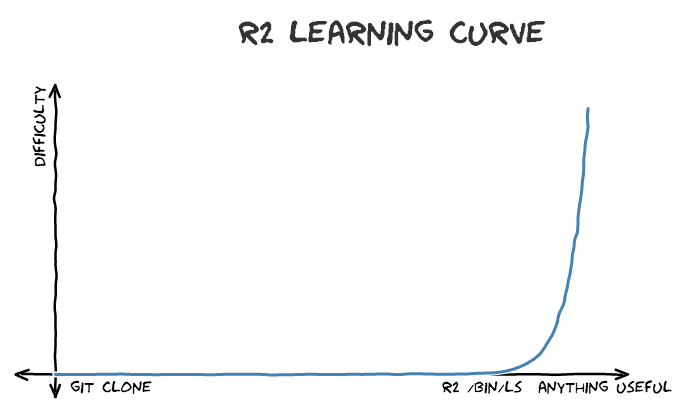
It is important to note that r2’s learning curve is pretty steep – although it has an amazing GUI called Cutter, which I co-maintain, it is still young to compete with more mature RE applications such as IDA or Ghidra. The CLI, however, including its Visual Mode, is still the core of radare2 and where its power lays. Because of its complexity, I’ll try to make things as clear and simple as I can.
Getting radare2
Installation
Radare2’s development is pretty quick – the project evolves every day. Therefore it’s recommended to use the current git version over the release one. Sometimes the release version is less stable than the current git version because of bug fixes!
git clone https://github.com/radare/radare2.git cd radare2 ./sys/install.sh
If you don’t want to install the git version or you want the binaries for another machine (Windows, OS X, iOS, etc) download the release from github.
Updating
As I said before, it is highly recommended to always use the newest version of r2 from the git repository. All you need to do to update your r2 version from the git is to execute:
./sys/install.sh
And you’ll have the latest version from git. I usually update my version of radare2 in the morning, while watching cat videos.
Uninstalling
I Can’t think of a reason for you to uninstall radare2 so early in the article but if you do want to, you can simply execute:
make uninstall make purge
Getting Started
[!] Download the first challenge from here.
Now that radare2 is installed on your system and you have downloaded the binary, we are ready to start exploring the basic usage of radare2. I’ll work on a Linux machine but most of the commands and explanations (if not all of them) would be the same for Windows machines and others.
Command Line Arguments
As most command-line utilities, the best approach to reveal the list of the possible arguments is to execute the program with the -h flag.
r2 -h
I won’t paste here the full output. Instead, I’ll point out those which I usually use in my daily work:
Usage: r2 [-ACdfLMnNqStuvwzX] [-P patch] [-p prj] [-a arch] [-b bits] [-i file]
[-s addr] [-B baddr] [-m maddr] [-c cmd] [-e k=v] file|pid|-|--|=
- same as 'r2 malloc://512'
-a [arch] set asm.arch
-A run 'aaa' command to analyze all referenced code
-b [bits] set asm.bits
-B [baddr] set base address for PIE binaries
-c 'cmd..' execute radare command
-d debug the executable 'file' or running process 'pid'
-i [file] run script file
-k [OS/kern] set asm.os (linux, macos, w32, netbsd, ...)
-l [lib] load plugin file
-p [prj] use project, list if no arg, load if no file
-w open file in write mode
Continue reading